The United Arab Emirates (UAE) has become one of the most advanced countries in the world in recent years in terms of digitalization and technological transformation. As Dubai and Abu Dhabi continue their modernization process, ranging from smart city projects to blockchain-based public services, one of the most critical elements of this development has been their cybersecurity strategies. Increasing cyber
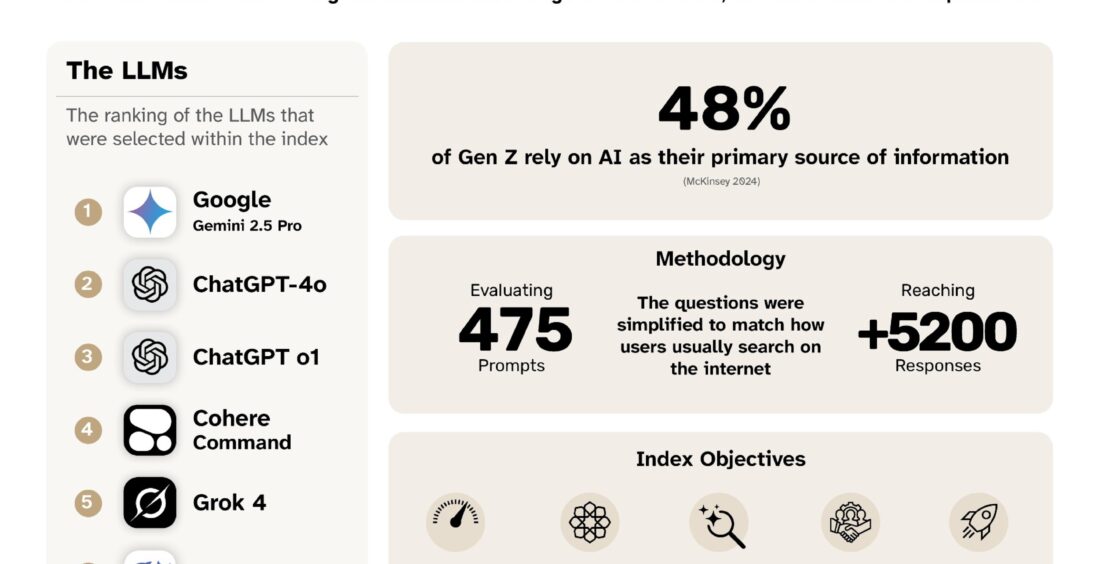
The UAE’s Artificial Intelligence, Digital Economy, and Remote Work Applications Office announced that Google Gemini has ranked first in the “AI in the Ring” Index, the world’s first benchmark designed to evaluate how effectively AI language models reflect Emirati culture, dialects, traditions, and national values through a challenge centered on cultural intelligence within the
A security vulnerability is a weak point in a system that allows attackers to perform actions such as unauthorized access, data theft, manipulation, or denial of service. The consequences of these vulnerabilities create serious technical and operational risks. Types of Security Vulnerabilities: Software Vulnerabilities: Coding errors or security weaknesses. For example, SQL injection, XSS (Cross-Site Scripting). System and Configuration Vulnerabilities: Misconfigured servers, default